When I run integration services package from inside of the windows box, they work. When I try to run them from outside of the box using my laptop, they fail. SQL Agent job works from either side.
Upon further investigation, I noticed these events in windows system event log;
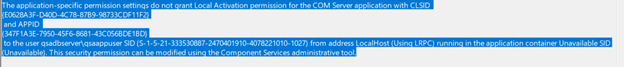
It seems that DistributedCOM component has permission issue; Add user’s to this window group;
Now we need to perform some DCOM component configuration to grant access to the Integration services service.
Run Dcomcnfg.exe. Dcomcnfg.exe provides a user interface for modifying settings in the registry.
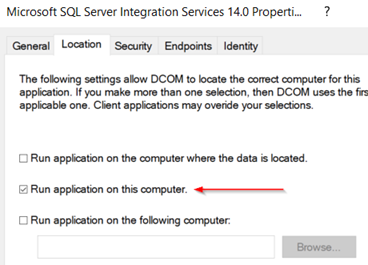
On the location tab, make sure “Run application on this computer” is checked.
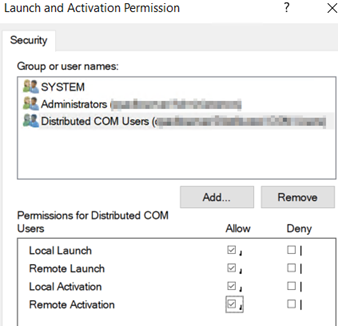
On the security tab, click Edit in the Launch and Activation Permission area. Add users and assign appropriate permissions, and then click ok.
Repeat above steps for Access permissions.
Restart database server.