You need to know the wattage and electric rate per kWh. For me the electric rate is (13 cents) .13 per kWh. Let’s find out how to get wattage.
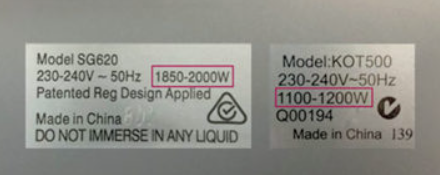
How can I find the wattage of a device?
Most devices have a label listing how many watts they use. You can find this wattage label either on the device (usually on the bottom or back) or in the owner’s manual.
Here is a list that shows the common wattage of everyday household devices. Though the wattage of your particular device may vary, it should give you a rough estimate.
| Coffee Maker | 900-1200 watts |
| Toaster | 800-1400 watts |
| Iron | 100-1800 watts |
| Ceiling fan | 65-175 watts |
| Space heater (40gal) | 4500-5500 watts |
| Hair dryer | 1200-1875 watts |
| Laptop | 50 watts |
| Computer monitor | 150 watts |
| Computer tower | 120 watts |
| Television 19″-36″ | 65-133 watts |
| Television 53″-61″ | 170 watts |
How to calculate kWh usage
To calculate your energy consumption, you’ll need to multiply an appliance’s wattage by the number of hours you use it in a day. That will give you the number of watt-hours consumed each day.
Calculate watt-hours per day
Device Wattage (watts) x Hours Used Per Day = Watt-hours (Wh) per Day
Example: A 125-watt television used three hours per day
125 watts x 3 hours = 375 Wh/Day
How many watts are in a kilowatt?
Your electricity bill is measured in kilowatt-hours (kWh), not watt-hours. One kilowatt is equal to 1,000 watts. To calculate how many kWh a device uses, divide the watt-hours from the previous step by 1,000.
Convert watt-hours to kilowatts
Device Usage (Wh) / 1000 (Wh/kWh) = Device Usage in kWh
Example: A television using 375 Wh of electricity per day
375 / 1000 = 0.375 kWh
Now that we know how many kWh the appliance uses per day, we can estimate that usage over a month. Let’s multiply by 30 days to simulate an average month.
Find your monthly energy usage
Daily Usage (kWh) x 30 (Days) = Approximate Monthly Usage (kWh/Month)
Example: A television using 0.375 kWh of electricity per day
0.375 kWh x 30 Days = 11.25 kWh/Month
In this example, a 125-watt television you use for three hours per day adds up to 11.25 kWh of energy per month. That is your television’s energy consumption.
To determine how much your appliances cost per month, multiply your electric rate by the estimated monthly usage from the steps above.
How much do appliances cost on my energy bills?
Monthly Usage (kWh) x Electric Rate ($/kWh) = Approximate Cost per Month
Example: A television using 11.25 kWh/Month with an electric rate of 10 cents per kWh ($0.10/kWh)
11.25 kWh x $0.10 = $1.13/Month
Based on these calculations, this television would cost you $1.13 per month. While that might not seem like much, the appliances and devices throughout your home will add up during a full month.
Your UPS would be another source of getting wattage. UPS will show the wattage number of all the devices that are connected. You can use that number to calculate your spending.
Reference